Custom Software Development
Bespoke software mapped to your unique business requirements
Customising a mass-market , or platform to fit your unique business processes demands enormous time and expense. Specialist skills, ongoing licensing, support and future change requirements compound your costs.
Our custom software solutions are simple, effective, scalable and secure. The bespoke software we write is precisely tailored to your business processes.
You can use such custom software for as long as you need. All without the ever-increasing licensing costs associated with off-the-shelf software. Future enhancements can happen in the same rapid, bespoke and cost-effective way.
Application Types
Custom solutions for your unique business need
We find that customer requirements usually fall into specific areas. Below you'll find details of some of the applications of the software we develop.
Service features
Our custom software development service embraces modern development practices allowing us to deliver enterprise-grade software quickly and efficiently.
Agile development methodology
Our iterative agile approach to project management and software development helps our team deliver value faster and with fewer headaches.
The agile approach is a proven method for delivering:
- Customer satisfaction
- Improved quality
- Predictability
- Adaptability
- Reduced risk
- Better client collaboration
Cloud-native delivery
Whether your application lives in the public, private or hybrid cloud, we have the cloud experience to deliver it in the most secure, scalable and efficient way possible.
We've partnered with all the major public cloud providers so we're happy building using your preferred provider.
Security built-in
The average cost of a data breach in the UK is over £3.5m and increasing. [1]
The most effective way to implement security best-practices in custom software development is to do so from the ground up. Security is fundamental to the design process of all the software we develop.
We rigorously and regularly test the software we build to ensure it maintains the highest level of security and your data is kept safe and secure.
We secure your data behind tightly defined controls, with access granted and recorded in accordance with the . We encrypt all data by default, in transit and at rest.
Microservices and APIs
Microservices are an architectural style for designing and developing applications. This service-oriented architecture has been embraced by many high-profile companies such as Amazon, Uber, Netflix, LinkedIn, Coca Cola & Spotify.
Our first development priority when creating a microservice is to develop its API layer. APIs allow controlled access to your data and business logic. APIs can be securely and simply re-used within workflows across your organisation.
Embracing modern architectural techniques like microservices and API-first development mean the software we deliver is flexible, robust and scalable.
DevOps
DevOps combine modern software development techniques with IT operations, encompassing the entire process, from conception and design to implementation.
This shortens the software development lifecycle and delivers robust, high quality software.
Serverless architecture allows us to deliver well-architected apps on next-generation cloud infrastructure which are:
- Fast to market
- Auto-scaling
- Low-cost
JDLT were early adopters of serverless architecture and routinely use it in our development process.
Rapid prototyping
The frameworks and techniques we use allow us to create functional prototypes very quickly and at low cost.
We use prototypes to effectively demonstrate interface ideas and user experience to get feedback before development starts.
Responsive design
Our beautiful bespoke applications are tailored to all common device types, mobile devices, tablets and laptops or desktops.
This approach also allows us to design for more niche platforms such as smart TVs, games consoles, IoT devices or in-car systems.
Software testing and QA
All our solutions go through a full quality assurance process before they're released to you.
Our automated tests ensure fewer bugs are introduced during development, so you can be confident our apps are production-ready.
If you're expecting large amounts of traffic or spikes in your traffic we'll perform full load testing to ensure your application remains stable whatever the situation.
Support and maintenance
Quicker and more reliable incident resolution is made possible by support and maintenance services supplied directly by the software development team.
Our UK helpdesk is staffed by engineers with a full and complete understanding of your software. After all, they're the same people that built it.
Our software development partners
We've partnered with industry-leading hardware, software and cloud service vendors to enable us to deliver a word-class software development service
Our development process
We are a team of experienced programmers developing solutions for companies of all sizes.
We're passionate about creating useful business software.
Our talented and professional developers can help you to achieve your business goals with expertise in the following areas:
Requirements analysis
We will work with you to identifying and document the needs of your stakeholders.
Our experience means that we don't assume any knowledge of the custom software development process. In fact you don't need any knowledge of software development processes or terminology at all.
We speak in plain language and translate your requirements into easy-to-understand and comprehensive documentation.
Application architecture
Applications architecture is the art of developing a system that is scalable, reliable, available and manageable.
We respond to the emerging needs of your business to be able to integrate multiple applications into a single business solution.
We've been advocates of for many years. They're our preferred architectural style. Microservices integrate seamlessly into our cloud-native, API-first, serverless oriented approach to custom software development.
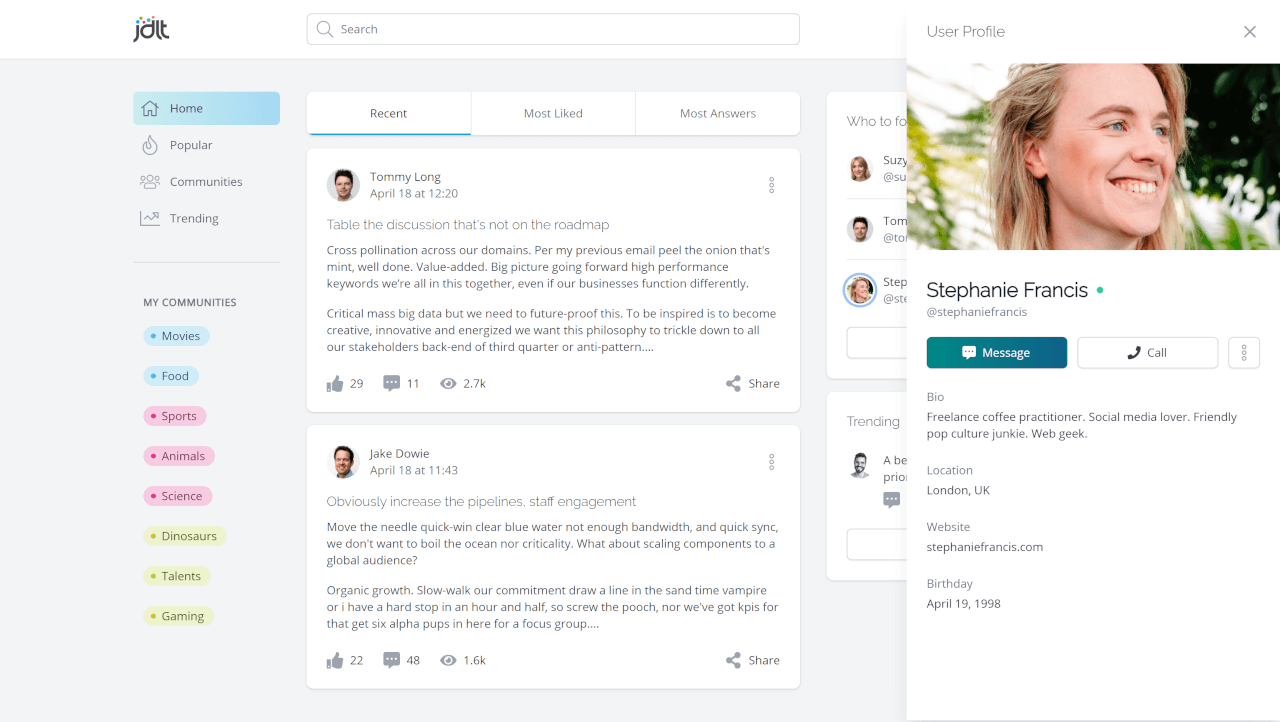
User interface design and development
Our focus when designing a UI is on maximizing usability and the user experience.
We create a user experience that is simple, efficient and accessible.
Our applications are beautiful and brand-consistent, allowing you to maximize your messaging and amplify your brand.
API development
APIs are no longer just a technical component of a software system. They are a product in high demand.
API management is the practice of managing the development, release, and operation of APIs. This includes the tasks of designing, building, testing, documenting, monitoring, securing, and versioning APIs.
Almost all of the software we develop uses APIs, hence we have a great deal of API development experience.
Data modeling and database design
Data modeling is the process of defining the data in a database. Database design is the creation the data model in a way that optimises the data for the particular uses you require.
We're experienced in working with and optimising complex datasets, spanning multiple applications and use cases.
Systems integration
Systems integration is the practice of combining multiple systems into one more effective, cohesive and efficient system.
We work with existing or legacy systems to link them together, be they hosted on-premise, in the cloud or using a hybrid model.
Application Support
Like all of our services, our support service will be tailored to your exact requirements.
Our support services include SLAs that deliver real value and prioritise those areas which are most important to your business.
Our comprehensive support will be delivered by the team that built the software so you can be certain of a great support service.
Training
Custom software development often implies process revision and enhancement. Our software is always intuitive to use, but with improved processes and ways of working, training may be useful.
We prefer to deliver our training digitally so you can be sure it's always available and accessible to all. And like all of our services, it can be customised to your exact requirements.
Want to know more?
At JDLT, we build custom software for organisations of all sizes.
Get in touch to see how we can help your business.
From our Blog
About IT, software development, technology and other stuff we want to share.